Network Traffic Analysis
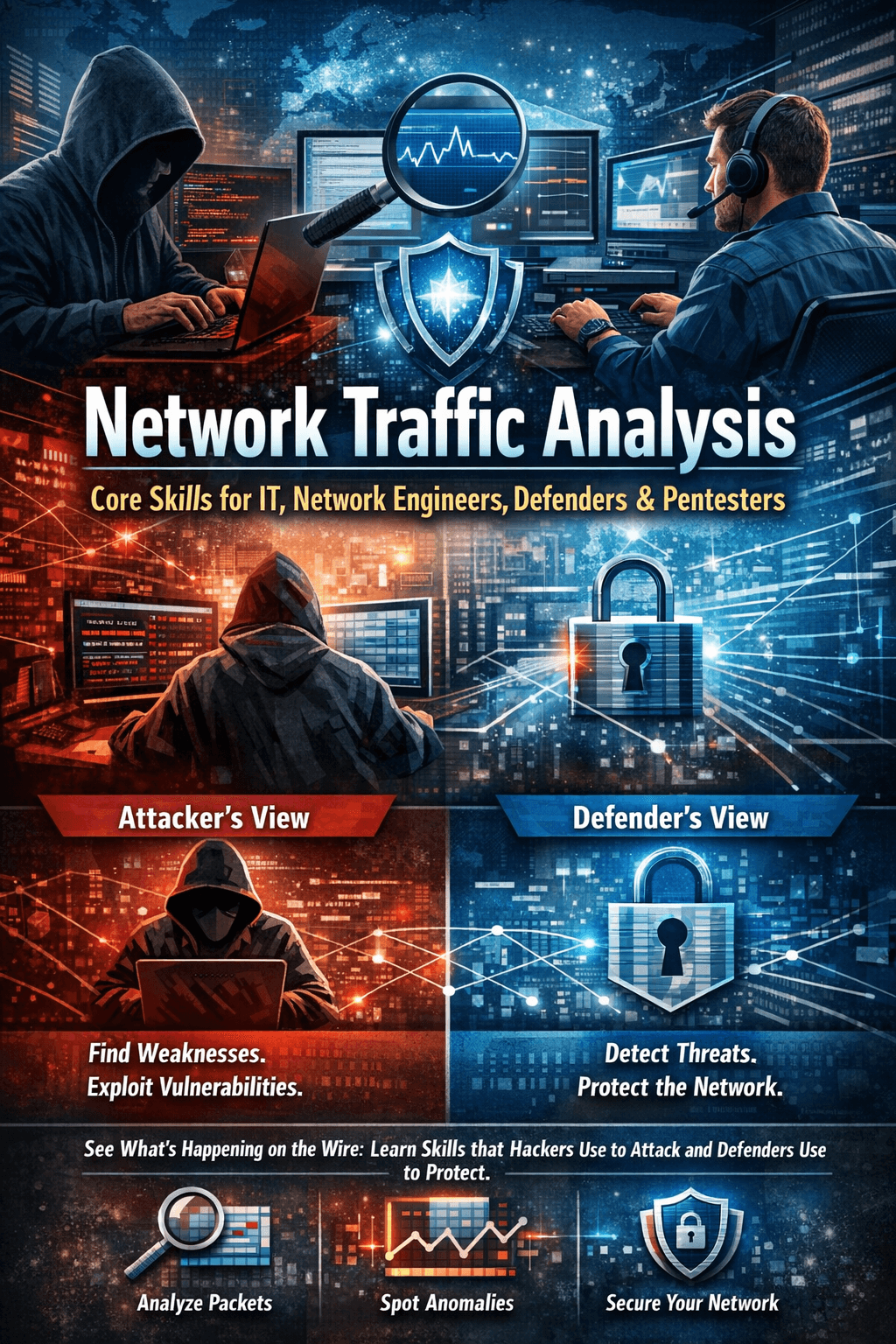
Core Skills for IT Technicians, Network Engineers, Defenders & Pentesters
Introduction
Every system tells a story.
Not in logs.
Not in dashboards.
But on the wire.
Every login, every file transfer, every scan, every misconfiguration — legitimate or malicious — becomes network traffic. Most people never look at it. The few who do gain something powerful: clarity.
Network traffic analysis is one of those rare skills that quietly separates average professionals from dangerous ones. It is the common ground where IT technicians troubleshoot outages, network engineers validate designs, defenders detect intrusions, and pentesters map attack paths. Different missions — same packets.
Attackers don’t guess. Defenders don’t rely on luck.
They observe, capture, filter, and understand what is really happening between systems.
If you’ve ever wondered:
How attackers move without being noticed
Why defenders miss obvious intrusions
Why “everything looks fine” while the network is compromised
Or why good engineers naturally become strong security analysts
The answer is almost always the same: network visibility.
This article breaks down the core network traffic analysis skills, the tools and methodologies used across roles, and—most importantly—how attackers and defenders look at the same traffic in completely different ways.
Because once you can read the wire,
the network can’t lie to you anymore.
Why Network Traffic Analysis Matters
Network traffic analysis (NTA) allows professionals to:
Understand how systems really communicate
Detect misconfigurations and design flaws
Identify malicious behavior and attack paths
Validate security controls and detections
Reconstruct incidents and attack timelines
Whether you are fixing an outage or breaking into a domain, everything starts with traffic.
If you don’t understand network traffic, you are blind — no matter your role.
Core Network Traffic Analysis Skills
1. Strong Networking Fundamentals (Non-Negotiable)
Before tools, before alerts, before exploits — you must understand how traffic flows.
Core concepts include:
OSI & TCP/IP models
TCP vs UDP behavior
DNS resolution process
ARP, ICMP, DHCP
Routing vs switching
VLANs & segmentation
NAT & firewall logic
TLS/SSL basics
Without this foundation, packet analysis becomes random clicking instead of analysis.
2. Packet-Level Thinking
A skilled analyst can answer:
Who initiated the connection?
On which port and protocol?
Was the traffic encrypted?
Did the handshake succeed?
What failed — and why?
This applies equally to:
A printer not responding
Malware beaconing outbound
A reverse shell failing to connect
An authentication error in Active Directory
Packets explain everything.
3. Traffic Pattern Recognition
Over time, professionals learn to recognize:
Normal vs abnormal traffic
Human vs automated behavior
Beaconing patterns
Scanning activity
Lateral movement indicators
This skill is built through repetition and exposure, not theory alone.
Tools Used for Network Traffic Analysis
Core Tools (All Roles)
| Tool | Purpose |
| Wireshark | Deep packet inspection |
| tcpdump / tshark | Command-line packet capture |
| netstat / ss | Connection visibility |
| nmap | Traffic generation & scanning |
| Firewall logs | Traffic allow/deny decisions |
| SPAN / TAP | Traffic mirroring |
Defender & SOC Tools
| Tool | Purpose |
| Zeek (Bro) | Protocol-level traffic analysis |
| Suricata / Snort | IDS / IPS detection |
| SIEM | Log and traffic correlation |
| NetFlow / IPFIX | Traffic metadata |
| EDR network telemetry | Endpoint network visibility |
Attacker / Pentester Tools
| Tool | Purpose |
| Wireshark / tcpdump | Payload & protocol analysis |
| Responder | LLMNR / NBNS poisoning |
| Impacket | SMB / Kerberos interaction |
| C2 frameworks | Beacon & channel analysis |
| Proxychains / Burp | Traffic interception |
Attackers and defenders often use the same tools — only the intent differs.
Network Traffic Analysis Methodology
This methodology applies to both offense and defense.
1. Visibility
What traffic can I see? From where?
2. Baseline
What does normal look like?
3. Filtering
Reduce noise by protocol, IP, port, or time.
4. Correlation
Network data alone is never enough.
5. Interpretation
Why does this traffic exist?
6. Action
Block, alert, fix, exploit, pivot.

How Attackers See Network Traffic
Attackers see traffic as opportunity.
They look for:
Clear-text credentials
Weak or legacy protocols
Misconfigured services
Trust relationships
Internal visibility after compromise
Attacker Mindset
“What can this traffic reveal about the environment?”
Examples:
DNS leaks internal domain structure
SMB traffic exposes Active Directory design
Kerberos errors reveal privilege boundaries
ICMP maps reachable networks
Firewall rules expose segmentation flaws
Traffic guides stealth, persistence, and lateral movement.
How Defenders See Network Traffic
Defenders see traffic as evidence.
They look for:
Deviations from baseline
Unauthorized protocols
Suspicious destinations
Beaconing behavior
East-west movement
Defender Mindset
“What does not belong here?”
Examples:
Workstations talking SMB to each other
DNS tunneling patterns
Long-lived outbound connections
Rare or suspicious user agents
Authentication outside business hours
Traffic tells the truth — if you know how to read it.
IT Technicians & Network Engineers Perspective
For IT and network engineers, traffic analysis is about reliability and stability.
They analyze:
Packet loss
Latency and jitter
MTU mismatches
Routing issues
Firewall misconfigurations
Many security incidents are discovered during troubleshooting, not hunting.
Strong engineers naturally become strong defenders.
Common Mistakes
Jumping to tools without understanding protocols
Ignoring encrypted traffic metadata
Analyzing packets without context
Failing to establish a baseline
Treating NTA as “security-only”
How to Build This Skill Practically
Analyze traffic in your own lab
Capture normal and broken scenarios
Observe:
AD logins
File transfers
VPN connections
Malware simulations
Compare normal vs attack traffic
Write short analysis reports
Final Thought
Network traffic analysis is not role-specific.
It is a core technical skill.
IT technicians use it to fix
Network engineers use it to design
Defenders use it to detect
Pentesters use it to exploit
The packets never lie.
Only your interpretation can.