How to install Metasploitable2 on docker — step-by-step

Did you ever want to test some technologies or Vulnerable labs at on place without the need to setup a separate virtual machine, that were Docker comes to help you setup those labs just in your attacking VM (kali parrot or exegol) or test VM.
Another point to take into consideration from a pentesting point of view is the fact that you will have to run your vulnerable VM inside of an isolated Docker Network (don’t expose it to the public internet), then use a pentest machine (Kali, for example) to test against it. Below I give the commands, a docker example, security notes, and clear definitions for every term used.
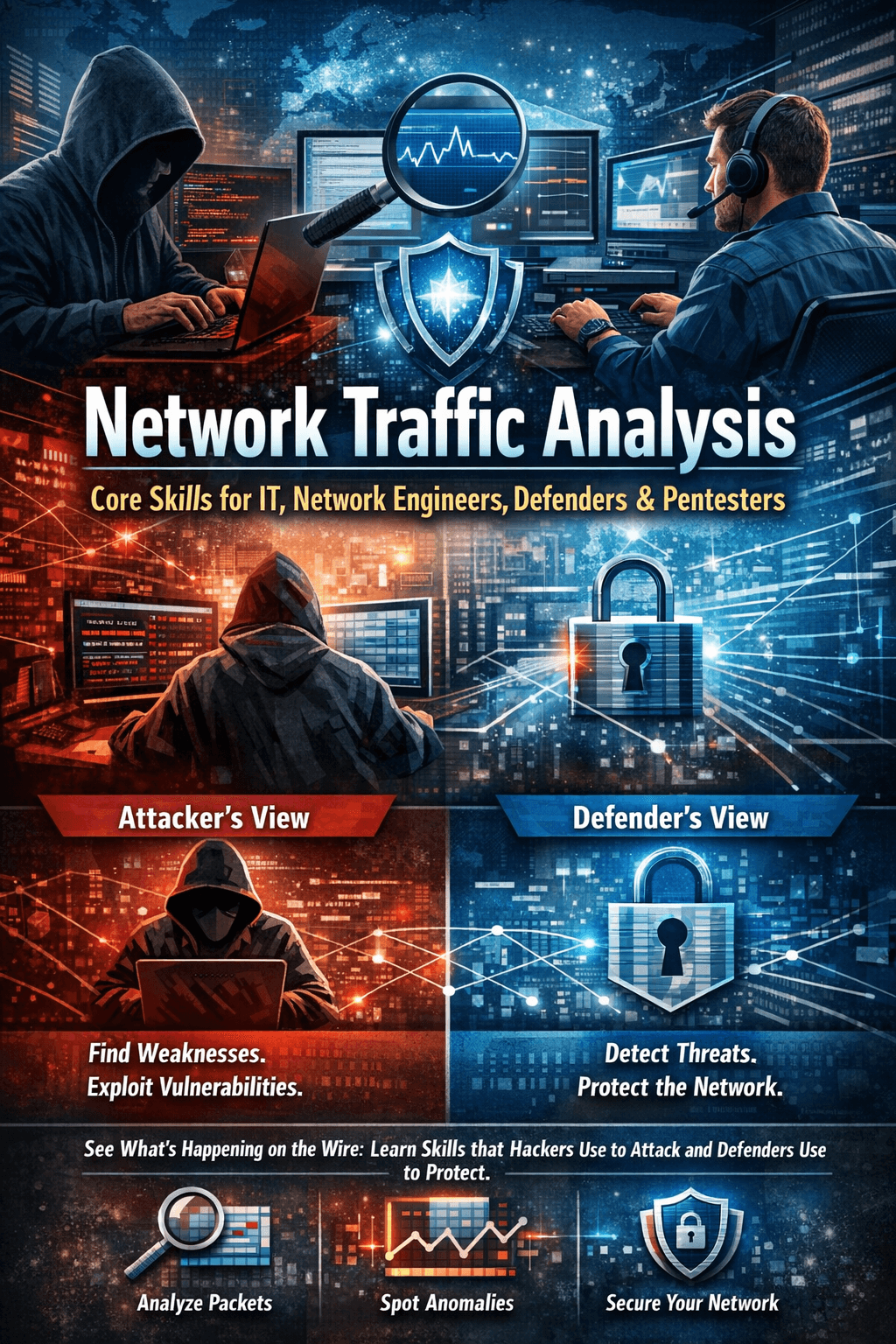
What is Metasploitable?
Metasploitable is an intentionally vulnerable virtual machine/image created for learning and practicing penetration testing. It’s purposely full of old/unpatched services so students can safely practice finding and exploiting vulnerabilities. Use it only in isolated labs.
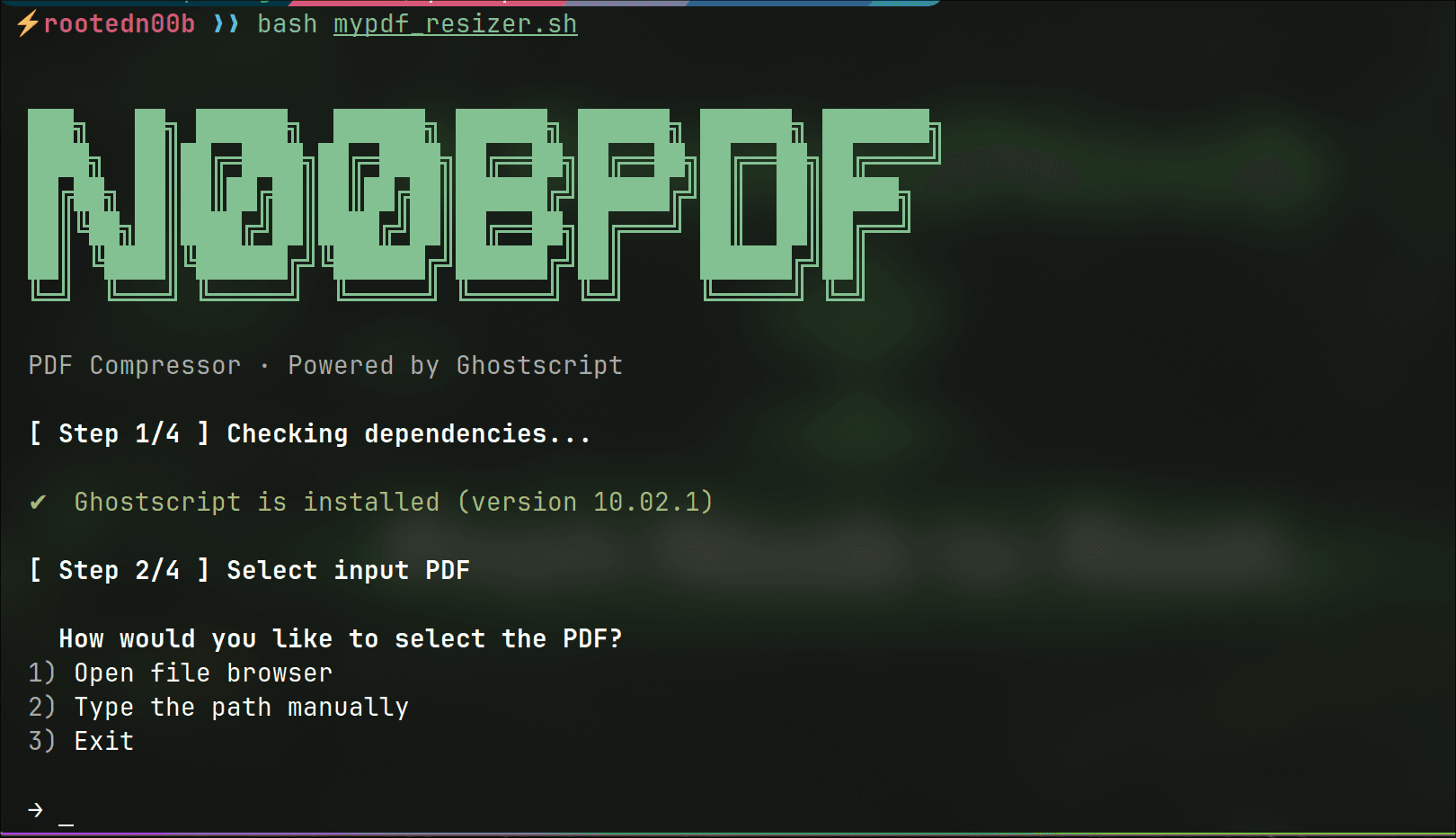
Quick install (Metasploitable2 Docker image)
Install Docker (if you don’t already).
On Linux: follow the official Docker docs (install
dockerand optionallydocker-compose).sudo apt install docker.io
Pull the image from Docker Hub (example image that many guides use):
docker pull tleemcjr/metasploitable2(Other community images exist; pick a trusted source or build your own from Metasploitable sources.) Docker Hub - Metasploitable2
Run a container in an isolated network (recommended):
# create a user network for your lab docker network create pentest-lab # pentest-lab refer to the name of your docker NIC
Run the container and attach the network to it
docker run -it --rm --name metasploitable2 -h metasploitable-hotname --network pentest-lab tleemcjr/metasploitable2
Find the container IP (After command successful you will prompt a shell on the metasploitable machine):
ifconfigLogin info (classic for Metasploitable2): username
msfadmin, passwordmsfadmin.
Security and best practices (must-read)
Do not expose Metasploitable to the public internet (no port publishing with
-punless you know what you’re doing). Run it on an isolated Docker network. EducativeTreat Metasploitable as untrusted code — it runs vulnerable services; run in a throwaway VM or on a dedicated lab machine.
Consider snapshots or ephemeral containers: destroy and recreate the container between lessons.
If you need reproducible builds, consider building your own Dockerfile from the Metasploitable3 project or sources rather than using random hub images.
Common variants / images
Metasploitable2 — older, classic vulnerable Linux VM; widely used in training.
Metasploitable3 — newer, built from scratch (Ubuntu/Windows flavors). There are community Docker builds and the official repo to build VMs. If you want an up-to-date vulnerable target you may prefer Metasploitable3
Glossary
Docker
Containerization platform that runs applications (and their dependencies) in lightweight, isolated environments called containers. Think of it like a very small virtual machine that shares the host OS kernel.Image
A read-only template that contains the file system and configuration for a container. Youpullimages from registries (e.g., Docker Hub) or build them locally. Example:tleemcjr/metasploitable2is an image.Container
A running instance of an image. Yourunan image to create and start a container. Containers have names (e.g.,metasploitable) and can be started, stopped, and removed.Docker Hub
A public registry where people publish Docker images so others can download them. There are official images and community images; trust matters.docker pull
Command to download an image from a registry to your host.docker run
Command to start a container from an image. Options include-d(detached),-it(interactive + TTY),--name(give it a name),--network(attach to a Docker network), and-p(publish container ports to the host).Port mapping (
-p)
Exposes container ports to the host machine (e.g.,-p 8080:80exposes container port 80 as port 8080 on the host). For Metasploitable, avoid mapping attackable ports to your public interfaces. Use internal Docker networking instead.Docker network / bridge network
A virtual network that Docker creates so containers can talk to each other. The default isbridge. Creating a dedicated user network (e.g.,pentest-lab) gives you isolation and easier service discovery by container name.docker-compose
A tool to define and run multi-container Docker applications using a YAML file. It simplifies starting multiple containers with one command.Image registry / trust
Community images on Docker Hub may be outdated or malicious; prefer official images or build your own from known sources. When using images for security training, verify the origin or build from the official Metasploitable project if you can.Metasploitable (2 / 3)
Intentionally vulnerable system images for learning pentesting. Metasploitable2 is an older Linux VM; Metasploitable3 is newer and hosted in Rapid7’s GitHub repo. Use them in isolated labs only.msfadmin:msfadmin
The default username:password for Metasploitable2 (common entry point for labs).
If you want to know how to install a container on Proxmox and deploy the metasploitable2 VM into it check the Homelab serie in the link below:
link: ==article coming soon==
Video Resource:
There are videos on youtube that reproduce the same thing I can refer that one: